Dell UEFI Secure Wipe
Earlier this month I needed to return a Dell laptop, which I had been testing via their corporate “try before you buy” scheme.
Historically, I would use a tool such DBAN, GParted or a Linux Live Environment to complete a secure wipe, protecting any sensitive corporate data.
Unfortunately, these traditional tools were designed to erase mechanical Hard Disk Drives (HDD), otherwise known as “spinning rust”. In the era of Solid State Drives (SSD), modern storage controllers continuously optimise data to improve performance, making these traditional tools less effective.
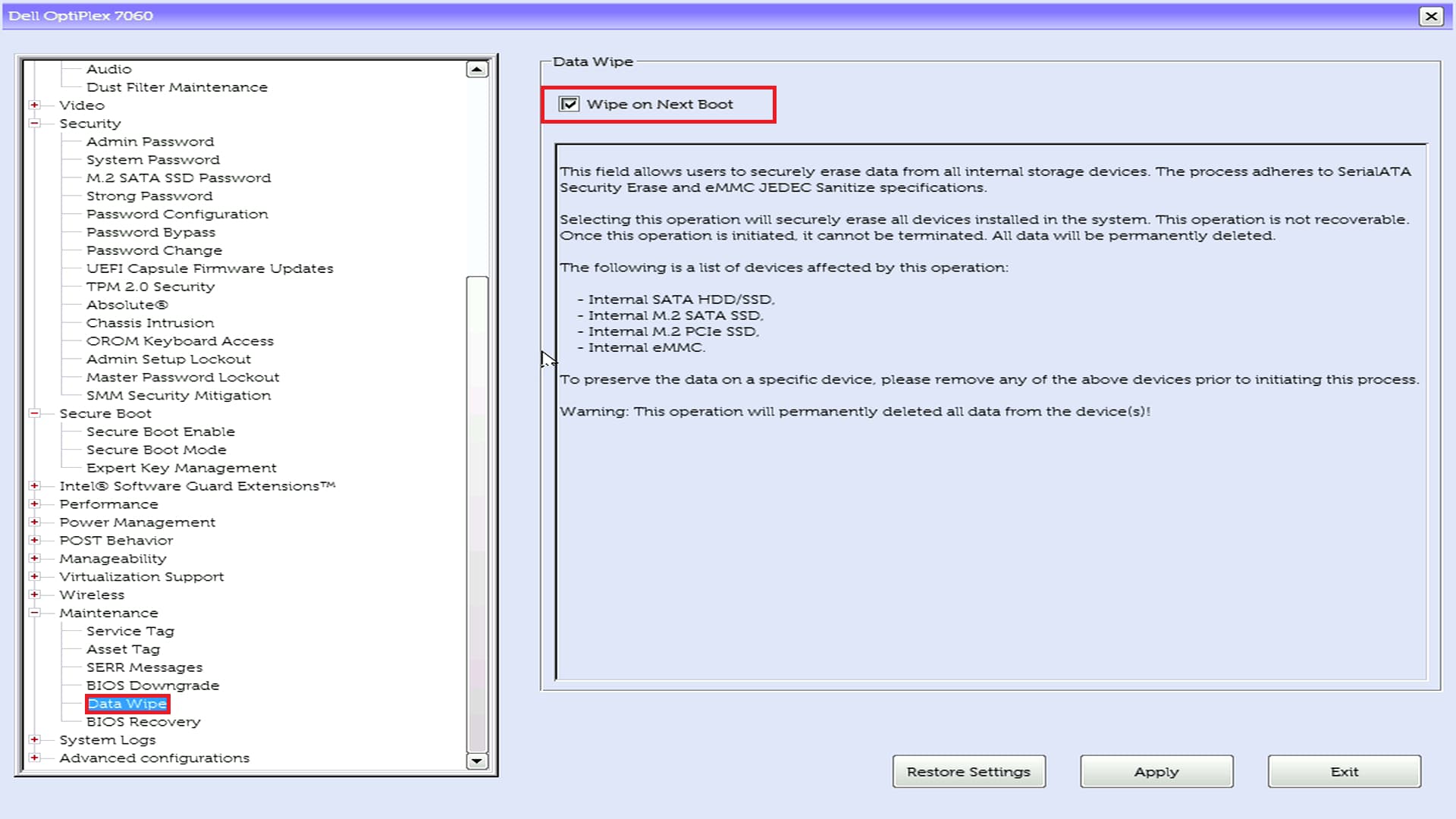
Thankfully, I was pleasantly surprised to learn that Dell laptops manufactured after 2016 include a secure wipe tool accessed via UEFI BIOS, which supports both HDD and SSD. The website “Dell Windows Installation Guide” includes an exellent step-by-step guide.
If the laptop includes an HDD (unlikely in 2021), the secure wipe process defaults to a traditional method, where each bit is zeroed individually. This process is time-consuming (multiple hours) and write intensive, but is effective.
If the laptop includes an SSD, the secure wipe process applies a voltage spike to the drive, which simultaneously zeros all data. This modern method is very fast (almost instant), but highly effective and avoids the intensive writes that can degrade/damage a drive.
Therefore, if you need to secure erase a modern Dell laptop, I would highly recommend using the UEFI BIOS tool (available in SMBIOS Version 2.9 or later). In the context of an SSD, it is fast, write efficient and highly effective.