Manjaro Full Disk Encryption
Manjaro is a great Linux distribution, delivering an opinionated Arch Linux experience that simplifies the setup and daily management.
One frustration, unlike Debian-based Linux distributions (e.g. Ubuntu, Pop!_OS), there is no “one-click” option to enable full disk encryption as part of the initial setup.
In 2021, I consider full disk encryption a foundational requirement, especially with modern hardware-accelerated encryption that mitigates any historical performance impact.
Thankfully, there is a workaround for Manjaro. It is not perfect, but certainly better than no encryption.
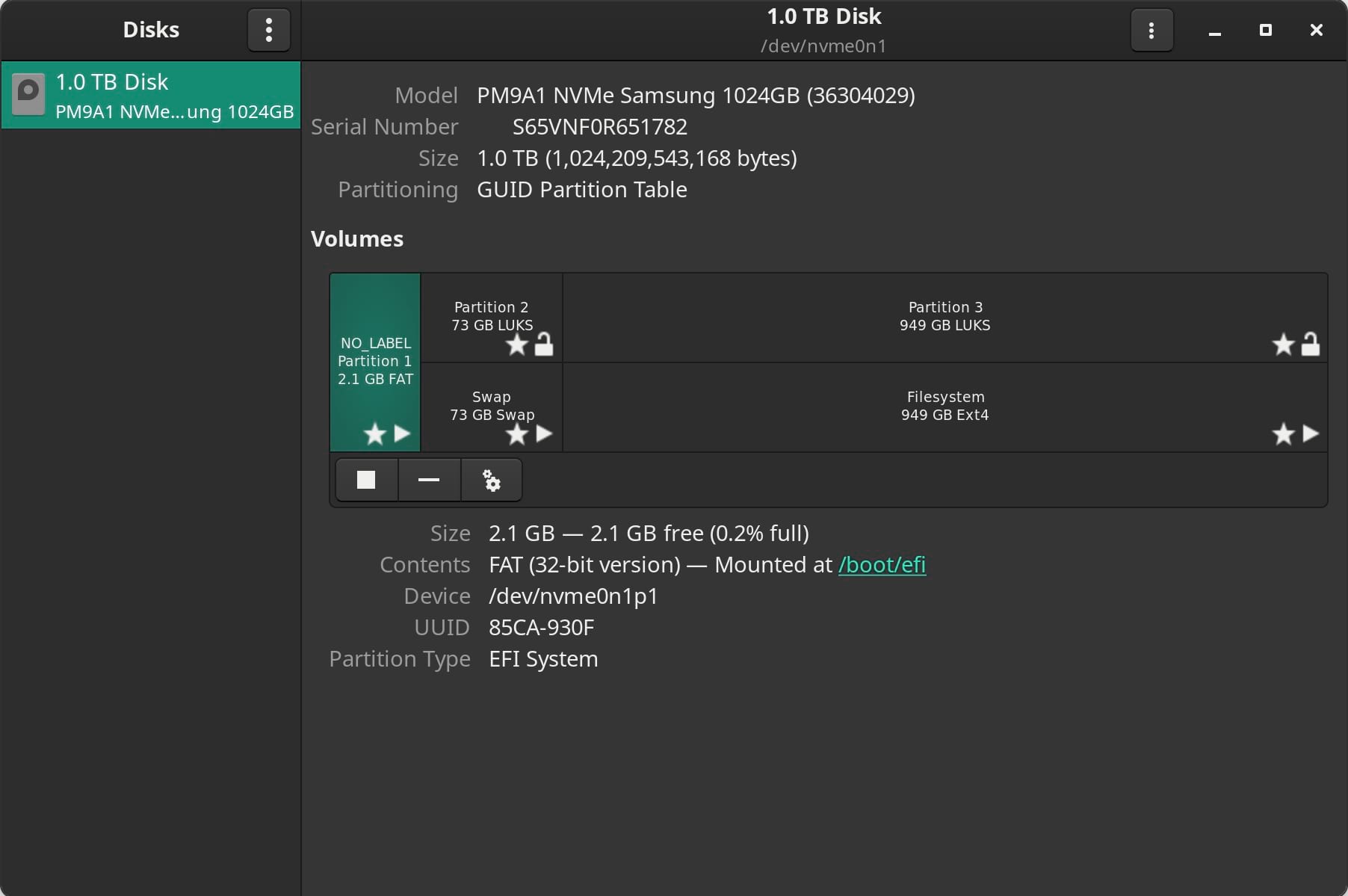
The approach is to manually partition the disk to include a small unencrypted boot partition. This partition is only used to boot the operating system, with all other partitions (storing the operating system, data and swap) being fully encrypted.
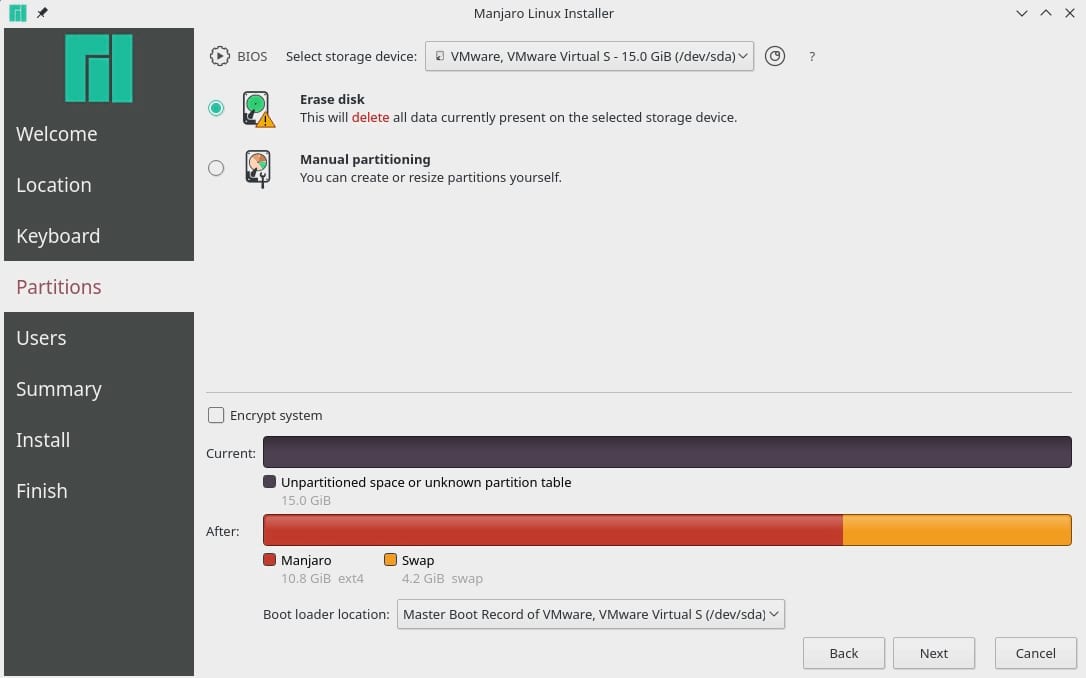
As part of the Manjaro setup process, when using the default installer, select “Manual Partitioning” from “Partitions”.
Delete all existing partitions and configure the following.
Partition 1
- Size: Minimum 300MB (Recommened 2GB)
- File System: fat32
- Mount Point: /boot/efi
- Flags: boot
Partition 2
- Size: System RAM + 5%
- File System: linuxswap + Encryption (luks)
- Mount Point:
- Flags: swap
Partition 3
- Size: Remaining Available Space
- File System: ext4 + Encryption (luks)
- Mount Point: /
- Flags: root
The SWAP partition is optional but recommended. If you plan to use hibernation, ensure you allocate enough capacity to cover your system memory, including a 5% buffer. For example, my system has 64GB RAM, therefore I allocate 70GB for SWAP.
The Linux Unified Key Setup (LUKS) is a platform-independent disk encryption specification, which is why any encrypted partition will show as “LUKS” instead of the chosen filesystem (e.g. EXT4).
LUKS is a fully open-source tool that has been the standard for disk encryption in Linux environments for many years. It sits in the kernel layer and encrypts storage at a disk block level, allowing for the transparent deployment of any file system.
Once configured, Manjaro will install as normal. Following a cold boot, the GRand Unified Bootloader (GRUB) will prompt for the disk encryption password.
Assuming the password is accepted the encrypted partitions will be opened and the Linux kernel will load as normal.
There are three minor challenges with this approach.
-
As the encryption password is requested by GRUB, before the operating system, any user-defined keyboard preferences are not loaded. Therefore, if your password includes special characters, you must know their location on a default US QWERTY keyboard.
-
Cold boot performance is slow, taking up to 30 seconds to accept the encryption password and open the encrypted partitions. Thankfully, this is only the case with a cold boot, which feels like a small price for encryption.
-
GRUB is not sophisticated when requesting the password. If the password is entered incorrectly, you must restart and try again.
Hopefully, the Majaro team will improve the full disk encryption experience over time, delivering a one-click option as part of the initial setup that also covers the boot partition.