Meltdown and Spectre
In early January, Google Project Zero researchers publicly disclosed a pair of security vulnerabilities known as Meltdown and Spectre, which impact almost every system across the world.
Meltdown and Spectre exploit vulnerabilities related to speculative execution in common processors (e.g. Intel Core Processors, etc.) The vulnerabilities affect the isolation between user applications and the operating system, and between different applications respectively.
As a result, an attacker can gain access to data processed by the underlying hardware, potentially including passwords, etc. This is especially concerning in multi-tenant environments with shared virtualised / containerised infrastructure (e.g. Cloud), where it might be possible to access data from other customers.
Although related, Meltdown and Spectre are separate vulnerabilities.
Meltdown
Meltdown breaks the isolation between user applications and the operating system, allowing a rogue process to read all memory without prior authorisation.
All Intel processors which implement out-of-order execution are likely affected by Meltdown, which essentially includes every processor since 1995 (excluding Intel Itanium and Intel Atom before 2013).
The name “Meltdown” highlights the fact that the vulnerability “melts” the security boundaries that are usually enforced by the hardware.
The Meltdown Whitepaper provides a detailed description of the vulnerability.
Spectre
Spectre breaks the isolation between different applications, allowing an attacker to manipulate a process into revealing its own data.
Almost every system worldwide is affected by Spectre, including desktops, laptops, tablets, smartphones, servers and cloud infrastructure.
The name “Spectre” describes the root cause, speculative execution.
The Spectre Whitepaper provides a detailed description of the vulnerability.
Conclusion
In summary, Meltdown and Spectre both use side channels to obtain data from a protected memory location. They are both widespread and difficult to mitigate, as traditional anti-virus software cannot easily differentiate malicious intent from regular usage.
It will likely take many weeks (maybe months) to fully mitigate Meltdown and Spectre, likely requiring a combination of operating system and firmware patches.
There is also a risk that the patches will have an impact on end-user performance, as specific features will need to be modified and/or disabled. Unfortunately, the severity of the impact will likely be workload specific, therefore difficult to predict without testing.
If you own a Mac or your PC that came pre-installed with Windows 10/S, you will likely receive the required patches automatically via your usual software update mechanism(s). However, if you are running older hardware or have a custom-built PC, you may need to manually download the patches from the hardware (e.g. Motherboard) manufacturers website.
Finally, the easiest way to understand if your system is vulnerable (at least on Windows), is to download and run InSpectre, which is a simple, but highly effective tool developed by security legend Steve Gibson.
As highlighted by the image below (my PC), InSpectre checks the status of the Meltdown and Spectre vulnerabilities, as well as evaluates the potential performance impact of the installed patches.
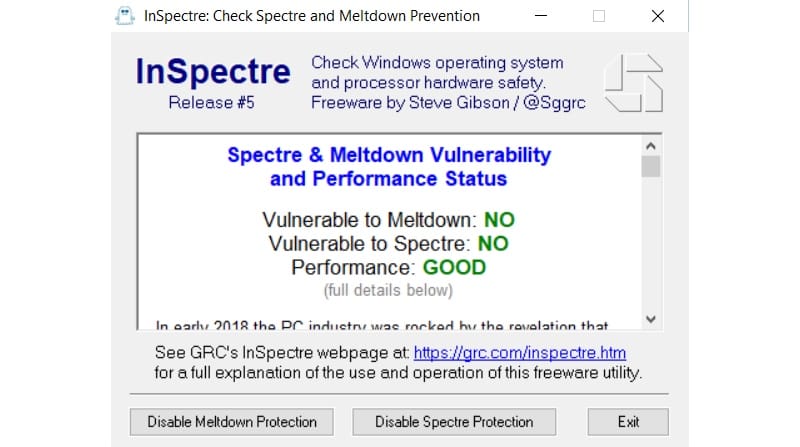
If you are using a Windows PC, I would highly recommend you download and run InSpectre now, followed by any required patches. If you are using a Mac, ensure you are running the latest operating system version (e.g. macOS High Sierra v10.13.3), which will include the latest mitigations, as provided by Apple.